Firewall > SSL Control
498
SonicOS Enhanced 4.0 Administrator Guide
–
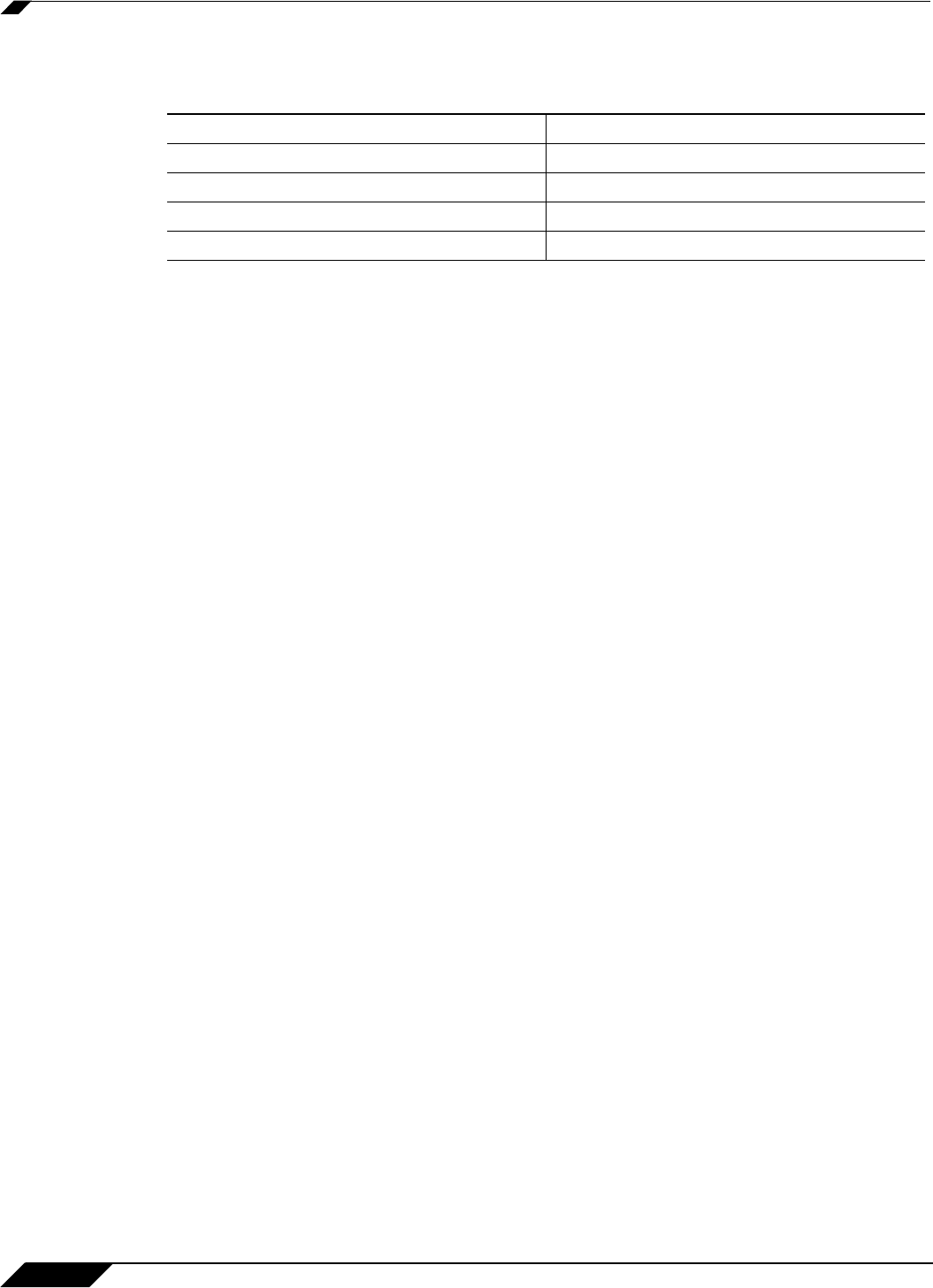
TLS – Transport Layer Security (version 1.0), also known as SSLv3.1, is very similar to
SSLv3, but improves upon SSLv3 in the following ways:
• MAC – A MAC (Message Authentication Code) is calculated by applying an algorithm (such
as MD5 or SHA1) to data. The MAC is a message digest, or a one-way hash code that is
fairly easy to compute, but which is virtually irreversible. In other words, with the MAC
alone, it would be theoretically impossible to determine the message upon which the digest
was based. It is equally difficult to find two different messages that would result in the same
MAC. If the receiver’s MAC calculation matches the sender’s MAC calculation on a given
piece of data, the receiver is assured that the data has not been altered in transit.
• Client Hello – The first message sent by the client to the server following TCP session
establishment. This message starts the SSL session, and consists of the following
components:
–
Version – The version of SSL that the client wishes to use in communications. This is
usually the most recent version of SSL supported by the client.
–
Random – A 32-bit timestamp coupled with a 28 byte random structure.
–
Session ID – This can either be empty if no Session ID data exists (essentially
requesting a new session) or can reference a previously issued Session ID.
–
Cipher Suites – A list of the cryptographic algorithms, in preferential order, supported
by the clients.
–
Compression Methods – A list of the compression methods supported by the client
(typically null).
• Server Hello – The SSL server’s response to the Client Hello. It is this portion of the SSL
exchange that SSL Control inspects. The Server Hello contains the version of SSL
negotiated in the session, along with cipher, session ID and certificate information. The
actual X.509 server certificate itself, although a separate step of the SSL exchange, usually
begins (and often ends) in the same packet as the Server Hello.
• Certificates - X.509 certificates are unalterable digital stamps of approval for electronic
security. There are four main characteristics of certificates:
–
Identify the subject of a certificate by a common name or distinguished name (CN or
DN).
–
Contain the public key that can be used to encrypt and decrypt messages between
parties
–
Provide a digital signature from the trusted organization (Certificate Authority) that
issued the certificate.
–
Indicate the valid date range of the certificate
• Subject – The grantee of a certificate identified by a common name (CN). When a client
browses to an SSL site, such as
https://www.mysonicwall.com, the server sends its
certificate which is then evaluated by the client. The client checks that the certificate’s dates
are valid, that is was issued by a trusted CA, and that the subject CN matches the
requested host name (i.e. they are both “www.mysonicwall.com”). Although a subject CN
SSL TLS
Uses a preliminary HMAC algorithm Uses HMAC as described in RFC 2104
Does not apply MAC to version info Applies MAC to version info
Does not specify a padding value Initializes padding to a specific value
Limited set of alerts and warning Detailed Alert and Warning messages


















