Survey the Network
Enterasys NAC Design Guide 4-3
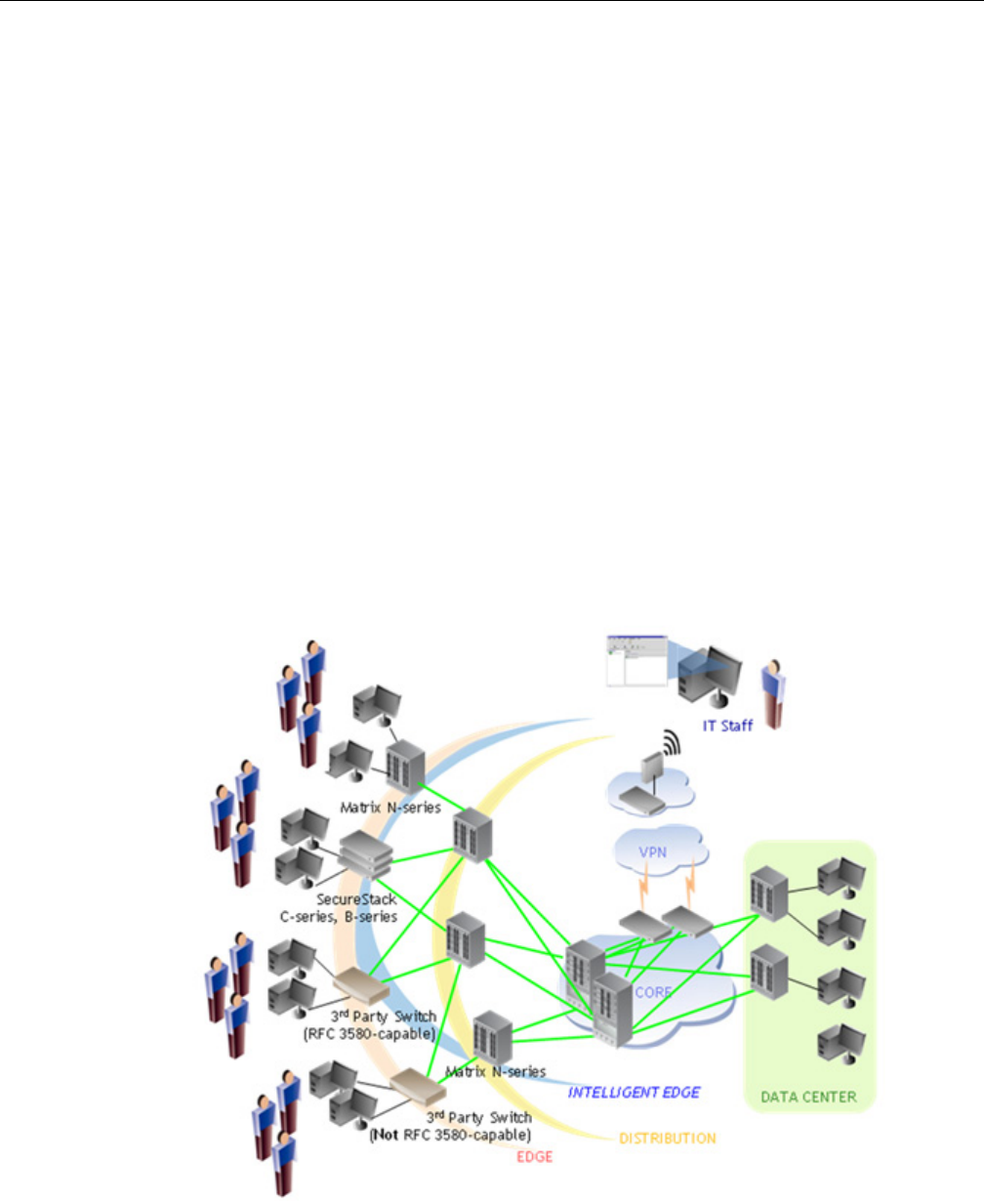
ThenetworkshowninFigure 4‐1below,illustratesthefollowingthreeexamplesofhowthe
intelligentedgecanbeimplementedinanetwork.
• Policy‐enabledEnterasysdevicesatthephysicaledgeofthenetwork.
TheSecureStackB2/B3,SecureStackC2/C3,andMatrixN‐seriesswitchesaretheintelligent
edgeofthenetwork
aswellasthephysicaledgeofthenetwork.Thesepolicy‐enableddevices
provideauthenticationandauthorizationviapolicyenforcementtotheconnectingend‐
systems.
•Third‐partyswitchesthatsupportRFC3580withdynamicVLANassignmentatthe
physicaledgeofthenetwork.
RFC3580‐compliantswitches(Enterasysandthird‐party),
arealsopartoftheintelligentedge
ofthenetwork,becausetheyareabletoauthenticateandauthorizeconnectingend‐systems
withaparticularlevelofnetworkaccess,usingdynamicVLANassignment.
•Policy‐enabledEnterasysdevicesatthedistributionlayerofthenetwork,upstreamfrom
non‐intelligentthird‐partydevices.
Theintelligent
edgeofthenetworkmayormaynotbethephysicaledgeofthenetworkwhere
end‐systemsactuallyconnect.TheMatrixN‐seriesswitchinthedistributionlayerofthe
network,upstreamfromthenon‐intelligentthird‐partydevice,isalsoconsideredpartofthe
intelligentedgeofthe
network.ThisisbecausetheMatrixN‐seriesswitchcanindividually
authenticateanduniquelyallocatenetworkresourcesfortheend‐systemsconnected
downstreamtothenon‐intelligentthird‐partyaccesslayerdevice.
Figure 4-1 Network with Intelligent Edge


















